Simple Install Guide
The following guide is for organizations with clusters that meet the prerequisites, and just want the direct instructions on installing Wallaroo in the target cluster.
This guides are targeted towards system administrators and data scientists who want to work with the easiest, fastest, and comprehensive method of running your own machine learning models.
Some knowledge of the following will be useful in working with this guide:
- Working knowledge of Linux distributions, particularly Ubuntu.
- A cloud provider including Google Cloud Platform (GCP), Amazon Web Services (AWS), or Microsoft Azure experience.
- Working knowledge of Kubernetes, mainly
kubectlandkotsorhelm.
The following guide is prepared for organizations that have an environment that meets the prerequisites for installing Wallaroo, and want to jump directly to the installation process.
For a complete guide that includes environment setup for different cloud providers, select the Wallaroo Enterprise Comprehensive Install Guide.
Some knowledge of the following will be useful in working with this guide:
- Working knowledge of Linux distributions, particularly Ubuntu.
- A cloud provider including Google Cloud Platform (GCP), Amazon Web Services (AWS), or Microsoft Azure experience.
- Working knowledge of Kubernetes, mainly
kubectlandkots.
For more information, Contact Us for additional details.
The following software or runtimes are required for Wallaroo 2024.2. Most are automatically available through the supported cloud providers.
| Software or Runtime | Description | Minimum Supported Version | Preferred Version(s) |
|---|---|---|---|
| Kubernetes | Cluster deployment management | 1.23 | 1.29 |
| containerd | Container Management | 1.7.0 | 1.7.0 |
| kubectl | Kubernetes administrative console application | 1.29 | 1.29 |
Install Wallaroo
Wallaroo installations are available via two methods:
kotsbased installations.helmbased installations.
Kubernetes Client Software Prerequisites
Before installing or upgrading Wallaroo, the administrative node managing the Kubernetes cluster will require these tools.
- kubectl
- For Kots based installs:
- kots Version
1.107.2
- kots Version
- For Helm installs:
helm: Install Helm- Minimum supported version: Helm 3.11.2
krew: Install Krewkrew preflightandkrew support-bundle. Install with the following commands:kubectl krew install support-bundlekubectl krew install preflight
- For Kots based installs:
The following are quick guides for installing kubectl for macOS.
To install kubectl on a macOS system using Homebrew:
Issue the
brew installcommand:brew install kubectlVerify the installation:
kubectl version --client
Kots Based Install of Wallaroo
Wallaroo kots based installations are broken up into two formats:
- Automated Install: Variables are passed to the installation process to auto-set the password, license file, and other settings before beginning the installation configuration process.
- Interactive Install: All parts of the installation process are performed through the browser interface.
Kots Install Guides
kots Quick Install Guide
The following are quick guides for installing kots for different operating systems. For more details, see the instructions for your specific environment.
IMPORTANT NOTE
As of this time, Wallaroo requires
kotsversion 1.107.2. Please verify that version is installed before starting the Wallaroo installation process.
Install
kotsby downloading the script and piping it into thebashshell, assumingcurlis installed:curl https://kots.io/install/1.107.2 | REPL_USE_SUDO=y bash
For instructions on updating the kots version for the Wallaroo Ops installation, see Updating KOTS.
Manual Kots Install
A manual method to install KOTS is:
Download from https://github.com/replicatedhq/kots/releases/tag/v1.107.2. Linux and MacOS are supported.
Unpack the release
Rename the kots executable to kubectl kots.
Copy the renamed kubectl kots to anywhere on the
PATH.Next, verify successful installation.
~ kubectl kots version Replicated KOTS 1.107.2
Automated Kots Wallaroo Install
To automatically install Wallaroo into the namespace wallaroo, specify the administrative password and the license file during the installation as in the following format with the following variables:
NAMESPACE: The namespace for the Wallaroo Enterprise install, typicallywallaroo.LICENSEFILE: The location of the Wallaroo Enterprise license file.SHAREDPASSWORD: The password of for the Kots Administrative Dashboard.
kubectl kots install wallaroo/2024-2 -n $NAMESPACE --license-file $LICENSEFILE --shared-password $SHAREDPASSWORD
For example, the following settings translate to the following install command:
NAMESPACE:wallaroo.LICENSEFILE:myWallaroolicense.yamlSHAREDPASSWORD:snugglebunnies
kubectl kots install wallaroo/2024-2 -n wallaroo --license-file myWallaroolicense.yaml --shared-password wallaroo
Interactive Kots Wallaroo Install
The Interactive Install process allows users to adjust the configuration settings before Wallaroo is deployed. It requires users be able to access the Kots Administrative Dashboard through a browser, typically on port 8800.
IMPORTANT NOTE: Users who install Wallaroo through another node such as in the single node installation can port use SSH tunneling to access the Kots Administrative Dashboard. For example:
ssh IP -L8800:localhost:8800
Install the Wallaroo Enterprise Edition using
kots install wallaroo/2024-2, specifying the namespace to install Wallaroo into. For example, ifwallaroois the namespace, then the command is:kubectl kots install wallaroo/2024-1 --namespace wallarooWallaroo Enterprise Edition will be downloaded and installed into your Kubernetes environment in the namespace specified. When prompted, set the default password for the Wallaroo environment. When complete, Wallaroo Enterprise Edition will display the URL for the Admin Console, and how to end the Admin Console from running.
• Deploying Admin Console • Creating namespace ✓ • Waiting for datastore to be ready ✓ Enter a new password to be used for the Admin Console: ••••••••••••• • Waiting for Admin Console to be ready ✓ • Press Ctrl+C to exit • Go to http://localhost:8800 to access the Admin Console
To relaunch the Kots Administrative Dashboard and make changes or updates, use the following command:
kubectl kots admin-console --namespace wallaroo
Initial Wallaroo Config
Once Wallaroo has been installed for the first time, we can perform initial configuration.
If Wallaroo Edition has not started, launch it with the following command:
❯ kubectl kots admin-console --namespace wallaroo • Press Ctrl+C to exit • Go to http://localhost:8800 to access the Admin ConsoleEnter the Kots Administrative Console address into a browser. You will be prompted for the default password as set in the step above. Enter it and select Log in.
Upload your license file. If the license file was already selected from the Automated installation, this step is skipped.
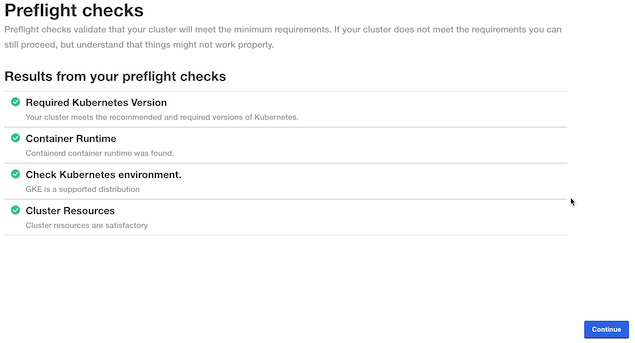
The Kots Administrative Console will run the preflight checks to verify that all of the minimum requirements are met. This may take a few minutes. If there are any issues, Wallaroo can still be launched but may not function properly. When ready, select Continue.
The Configure Wallaroo page will be displayed which allows you to customize your Wallaroo environment. The following are the minimum required settings.
Networking Configuration: Set whether the Wallaroo instance is available from outside the Kubernetes cluster, or only from within it.
- Ingress Mode for Wallaroo Endpoints:
- None: Services are local to the Kubernetes cluster.
kubectl-port forwardor some other means is required to access them. If all work will be done in-cluster, select this option. - Internal: An internal cloud load balancer and associated resources are created. Network users outside the Kubernetes cluster – but on the same internal network – can connect directly using DNS names, and do not need to use port forward or related configurations.
- External: An external, Internet-facing cloud load balancer, public IP, and associated resources are created. This is highly discouraged. Public DNS is also required. This is the default for Wallaroo Community Edition.
- Enable external URL inference endpoints: Creates pipeline inference endpoints. For more information, see Model Endpoints Guide.
- None: Services are local to the Kubernetes cluster.
- Ingress Mode for Wallaroo Endpoints:
From the Wallaroo Dashboard, select Config and set the following:
DNS Settings
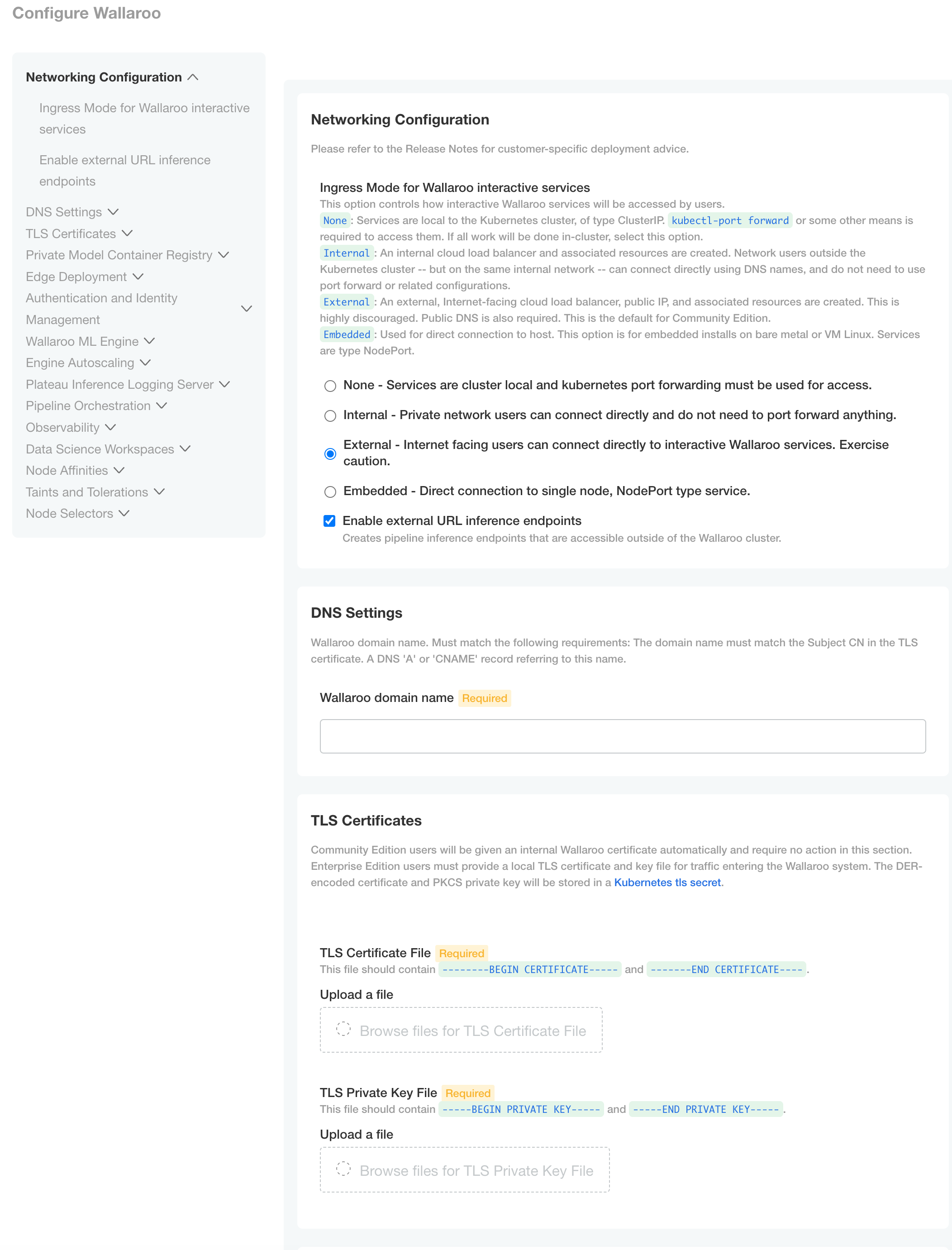
- Wallaroo domain name (Required): The domain for the Wallaroo instance.
TLS Certificates
- Use custom TLS Certs: Checked
- TLS Certificate: Enter your TLS Certificate (.crt file).
- TLS Private Key: Enter your TLS private key (.key file).
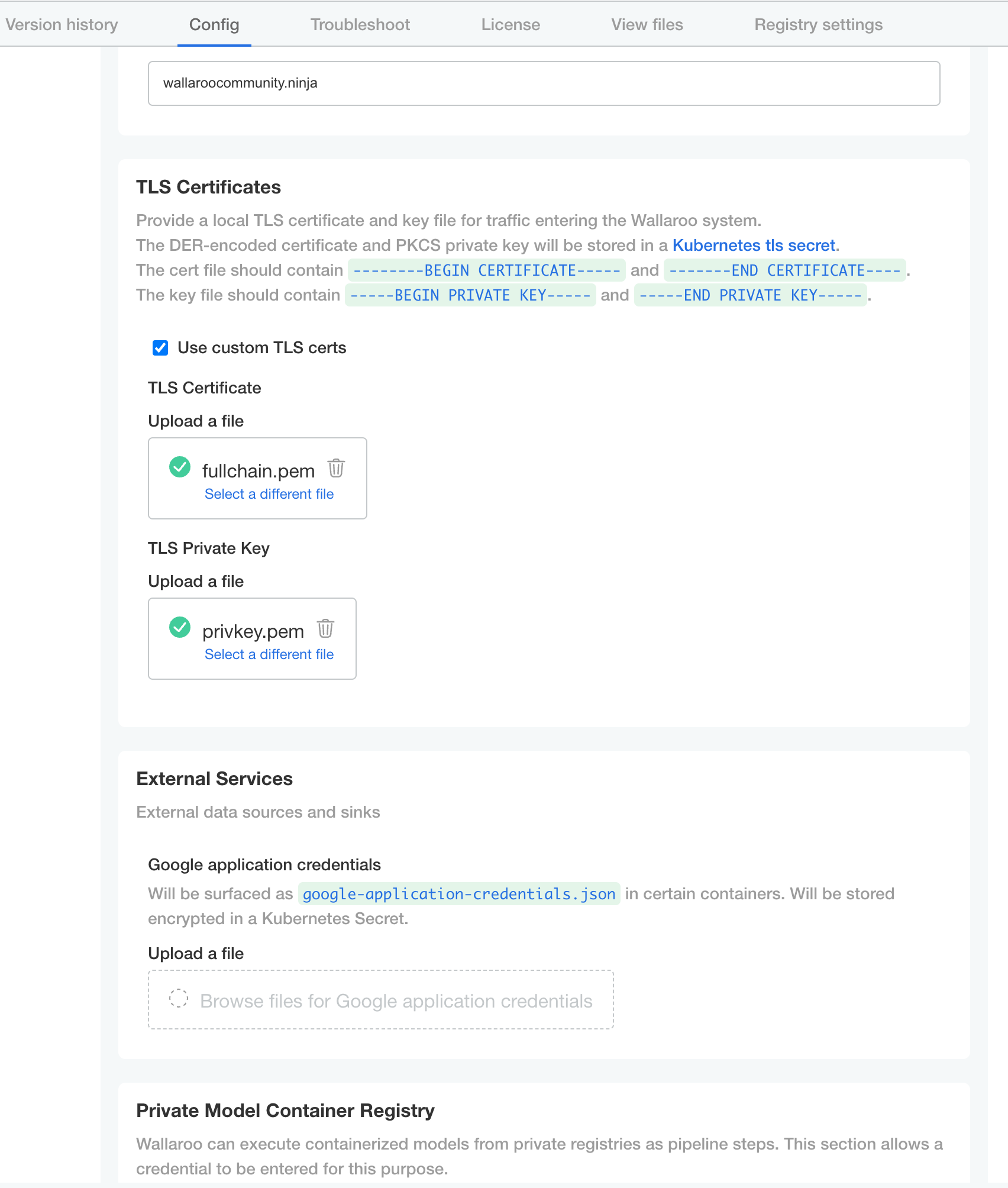
Once complete, scroll to the bottom of the Config page and select Deploy.
At this point, continue to Required Installation Configurations for the required configuration settings.
Edge Deployment Configuration
The following optional configurations to enable OCI Registry integration with Wallaroo for deploying models in edge and multi-cloud environments through Wallaroo. For more details, see Inference Anywhere.
To set the Edge Registry Settings through the Kots Administrative Dashboard:
Launch the Kots Administrative Dashboard using the following command, replacing the
--namespaceparameter with the Kubernetes namespace for the Wallaroo instance:kubectl kots admin-console --namespace wallarooOpen a browser at the URL detailed in the step above and authenticate using the console password set as described in the as detailed in the Wallaroo Install Guides.
From the top menu, select Config then scroll to Edge Deployment.
Enable Provide OCI registry credentials for pipelines.
Enter the following:
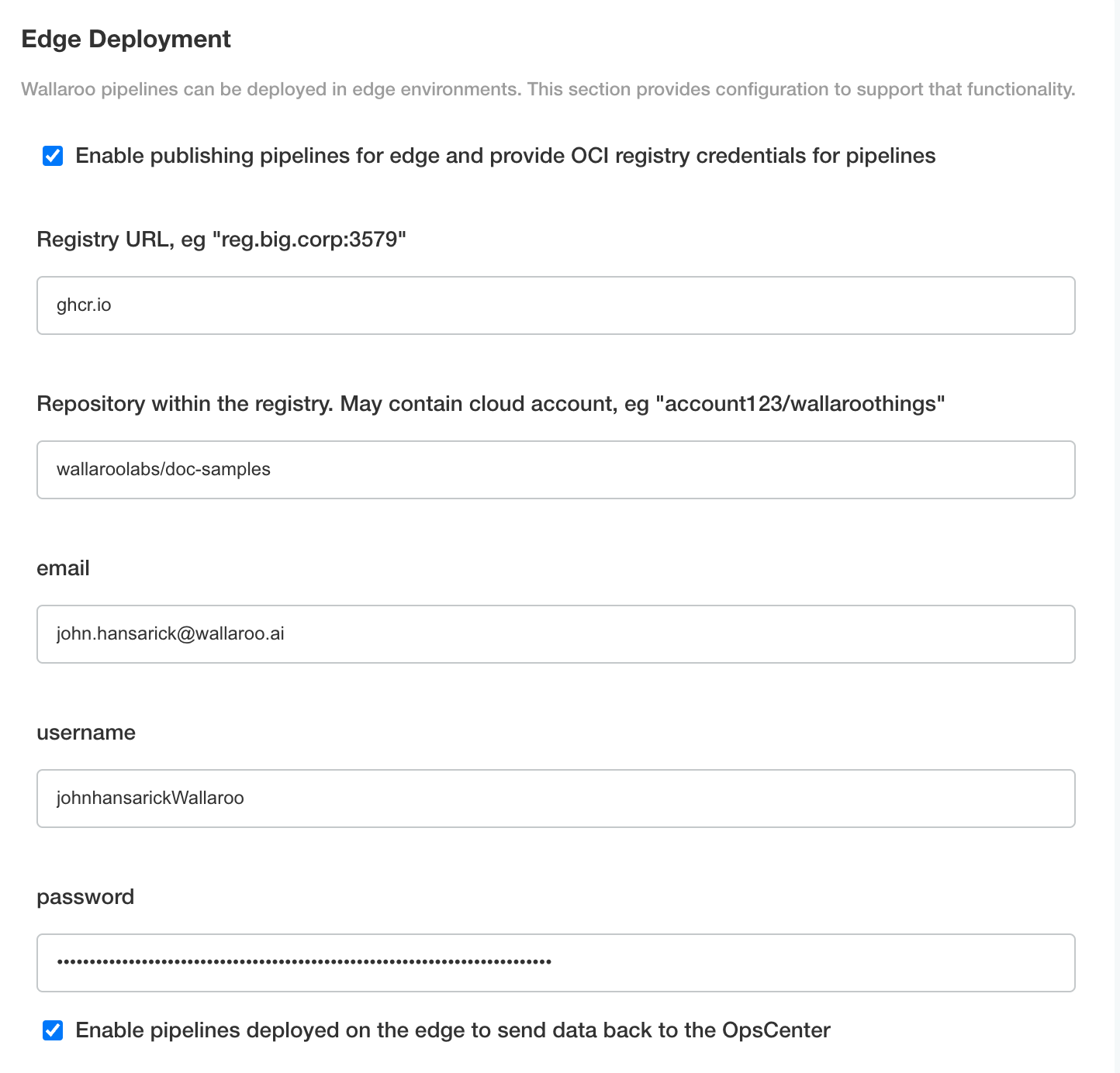
- Registry URL: The address of the registry service. For example:
us-west1-docker.pkg.dev. - email: The email address of the user account used to authenticate to the service.
- username: The account used to authenticate to the registry service.
- password: The password or token used to authenticate to the registry service.
- To enable edge observability, enable Enable pipelines deployed on the edge to send data back to the OpsCenter.
- Registry URL: The address of the registry service. For example:
Save the updated configuration, then deploy it. Once complete, the edge registry settings will be available.
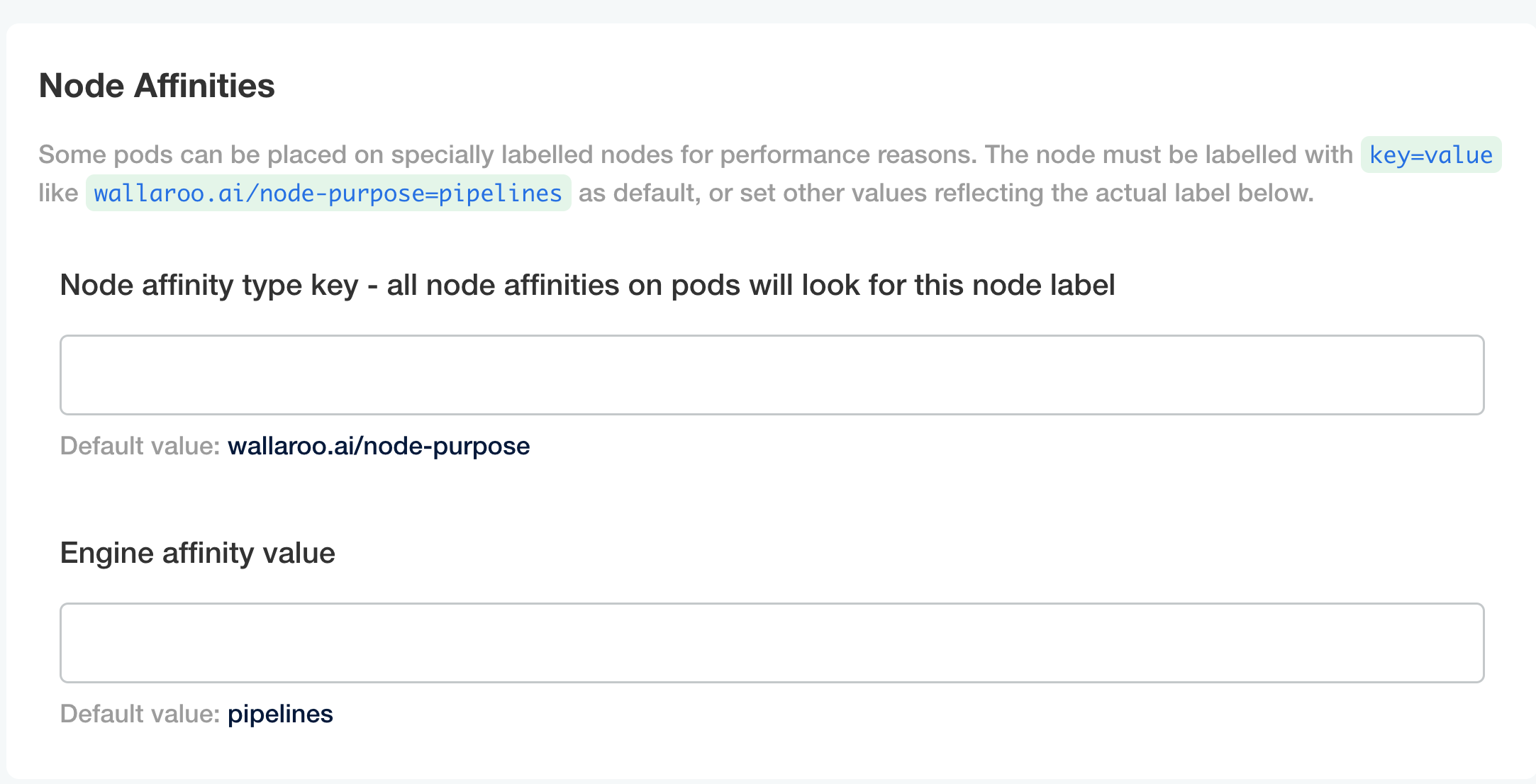
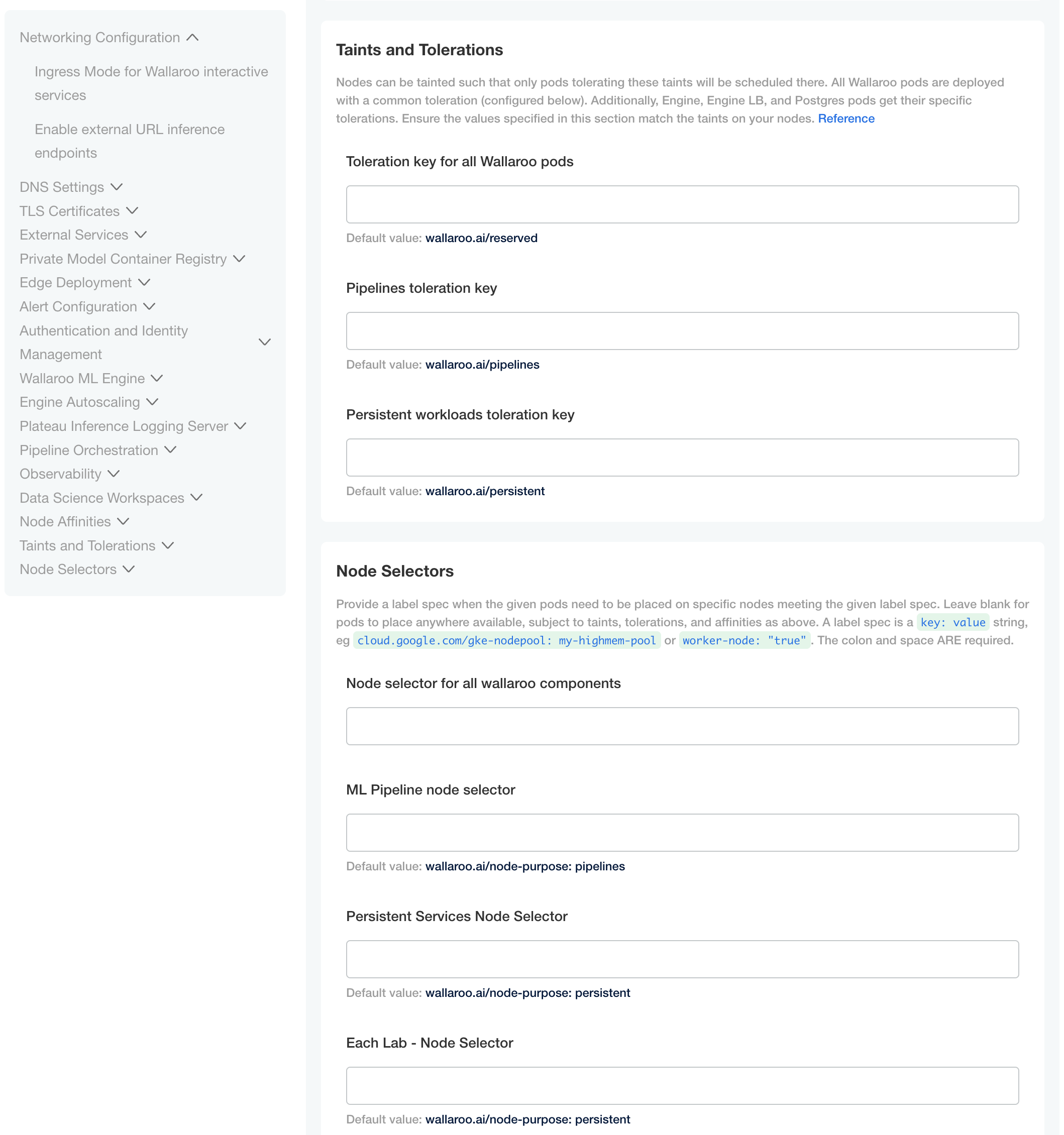
Custom Tolerations and Node Selectors Configuration
By default, the following taints and labels are applied to nodepools used for Wallaroo installations.
| Nodepool | Taints | Labels | Description |
|---|---|---|---|
| general | N/A | wallaroo.ai/node-purpose: general | For general Wallaroo services. No taints are applied to this nodepool to allow any process not assigned with a deployment label to run in this space. |
| persistent | wallaroo.ai/persistent=true:NoSchedule | wallaroo.ai/node-purpose: persistent | For Wallaroo services with a persistentVolume settings, including JupyterHub, Minio, etc. |
| pipelines-x86 | wallaroo.ai/pipelines=true:NoSchedule | wallaroo.ai/node-purpose: pipelines | For deploying pipelines for default x86 architectures. The taints and label must be applied to any nodepool used for model deployments. |
The specific nodepool names may differ based on your cloud services naming requirements; check with the cloud services provider for the nodepool name requirements and adjust as needed.
For organizations that use custom Kubernetes taints and labels for their nodepools, the tolerations and node selectors for Wallaroo services will have to be modified to match. For full details, see the Custom Taints and Labels Guide.
To modify the tolerations and node selector labels to match the taints and labels set for the nodepools:
- From the Kots Administrative Dashboard, select Config
- Update each of the following as needed:
Node Affinities:
Node affinity type key: Verify that the node affinity key matches the label for the nodepools.
Engine affinity value: Set the engine affinity - the affinity used for pipeline deployment - to match the label.
Taints and Tolerations. Set the custom tolerations to match the taints applied to the nodepools, and the node selectors to match the labels used for the nodepools.
Node Selectors: Update the node selector to match the custom nodepools labels for each service.
Helm Based Installation of Wallaroo
Installation Client Helm Requirements
The following software is required for the client with administrative access to the Kubernetes cluster that will host Wallaroo via Helm.
- For Helm installs:
helm: Install Helm- Minimum supported version: Helm 3.11.2
krew: Install Krewkrew preflightandkrew support-bundle. Install with the following commands:kubectl krew install support-bundlekubectl krew install preflight
The following details how to install Wallaroo via helm.
Wallaroo Provided Data
Members of the Wallaroo support staff will provide the following information:
- Wallaroo Container Registration Login: Commands to login to the Wallaroo container registry.
- Preflight verification command: The commands to verify that the Kubernetes environment meets the requirements for the Wallaroo install.
- Install Wallaroo Command: Instructions on installations into the Kubernetes environment using Helm through the Wallaroo container registry.
The following steps are used with these command and configuration files to install Wallaroo Enterprise via Helm.
Registration Login
The first step in the Wallaroo installation process via Helm is to connect to the Kubernetes environment that will host the Wallaroo Enterprise instance and login to the Wallaroo container registry through the command provided by the Wallaroo support staff. The command will take the following format, replacing $YOURUSERNAME and $YOURPASSWORD with the respective username and password provided.
helm registry login registry.replicated.com --username $YOURUSERNAME --password $YOURPASSWORD
Preflight Verification
IMPORTANT NOTE
The preflight test is not programmatically enforced during installation via Helm and should be performed manually before installation. If the Kubernetes environment does not meet the requirements the Wallaroo installation may fail or perform erratically. Please verify that all preflight test run successfully before proceeding to install Wallaroo.Preflight verification is performed with the following command format. The variables $LICENSE_CHANNEL and $VERSION is supplied by your Wallaroo support representative.
helm template oci://registry.replicated.com/wallaroo/$LICENSE_CHANNEL/wallaroo --version $VERSION | kubectl preflight -
For example, the $LICENSE_CHANNEL=2024-2 of 2024-2 and the $VERSION=2024.2.1
helm template oci://registry.replicated.com/wallaroo/2024-2/wallaroo --version 2024.2.1 | kubectl preflight -
This displays the Preflight Checks report.
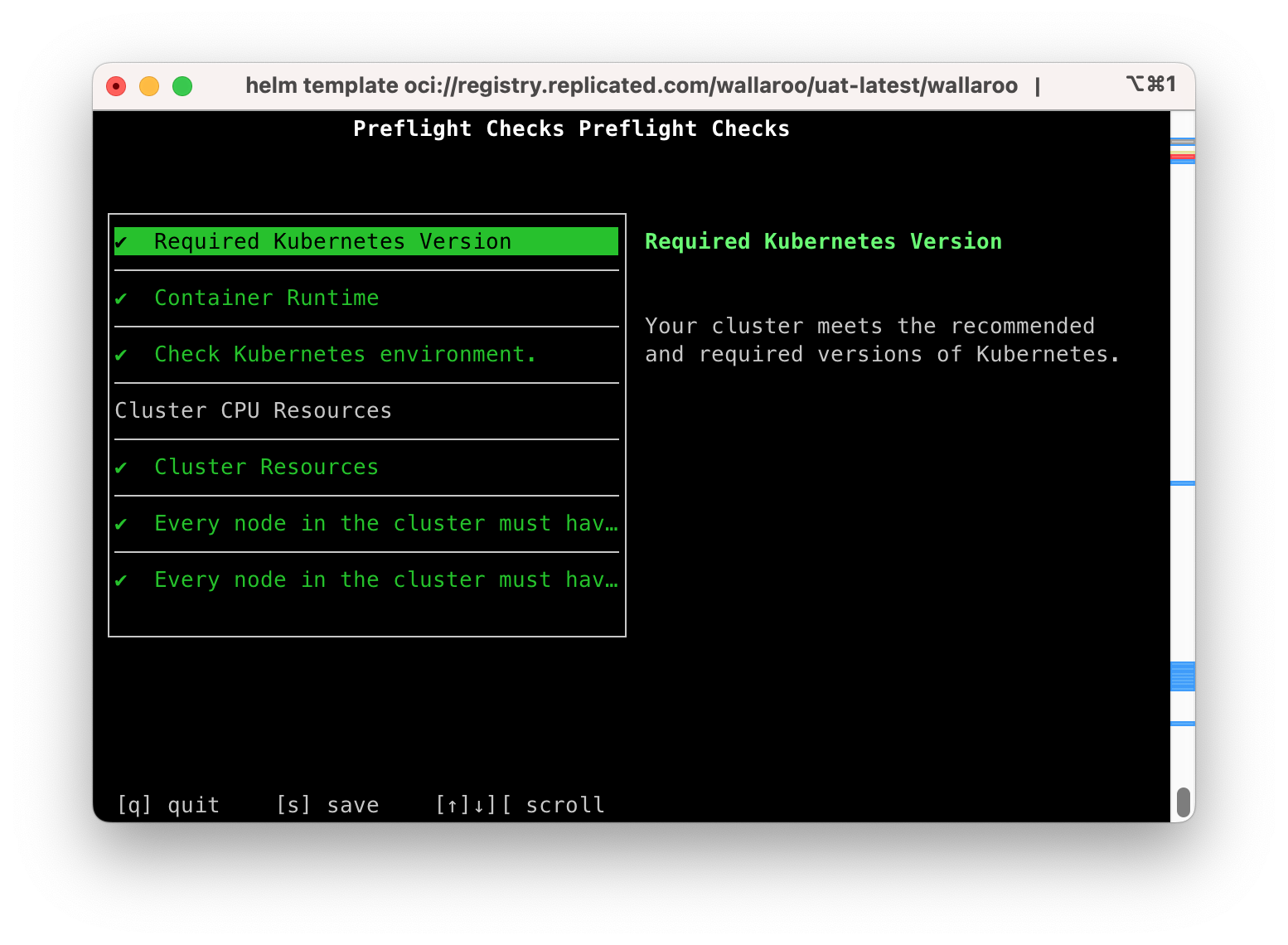
The following commands are available:
s: Save the report to a text file as the filepreflight-checks-results-DATETIME.txt. For example:preflight-checks-results-2024-03-19T13_30_41.txt.q: Exit the preflight report.Up ArroworDown Arrow: Scroll through the preflight elements and view the report details.
The following example shows a successful preflight test.
Preflight Checks Preflight Checks
Check PASS
Title: Required Kubernetes Version
Message: Your cluster meets the recommended and required versions of Kubernetes.
------------
Check PASS
Title: Container Runtime
Message: Containerd container runtime was found.
------------
Check PASS
Title: Check Kubernetes environment.
Message: GKE is a supported distribution
------------
Title: Cluster CPU Resources
Message:
------------
Check PASS
Title: Cluster Resources
Message: Cluster resources are satisfactory
------------
Check PASS
Title: Every node in the cluster must have at least 12Gi of memory
Message: All nodes have at least 12 GB of memory capacity
------------
Check PASS
Title: Every node in the cluster must have at least 8 cpus allocatable.
Message: All nodes have at least 8 CPU capacity
------------
Prepare Helm Installation
The following instructions detail how to install Wallaroo Enterprise via Helm for Kubernetes cloud environments such as Microsoft Azure, Amazon Web Service, and Google Cloud Platform.
Helm Network Configuration
apilb.serviceType settings have the following effects depending on whether they are installed on single node Linux installations, or part of a cloud Kubernetes installation.
| Setting | Single Node Linux | Cloud Kubernetes |
|---|---|---|
| Internal Only Connections | ClusterIP | ClusterIP |
| External Connections | NodePort | LoadBalancer |
Refer to the instructions for environment host for details on IP address allocation and support.
With the preflight checks and prerequisites met, Wallaroo can be installed via Helm through the following process:
Create namespace. By default, the namespace
wallaroois used:kubectl create namespace wallarooSet the new namespace as the current namespace:
kubectl config set-context --current --namespace wallarooSet the TLS certificate secret in the Kubernetes environment:
Create the certificate and private key. It is recommended to name it after the domain name of your Wallaroo instance. For example:
wallaroo.example.com. For production environments, organizations are recommended to use certificates from their certificate authority. Note that the Wallaroo SDK will not connect from an external connection without valid certificates. For more information on using DNS settings and certificates, see the Wallaroo DNS Integration Guide.Create the Kubernetes secret from the certificates created in the previous step, replacing
$TLSCONFIGwith the name of the Kubernetes secret, with the certificate file$TLSCERTand the private key$TLSKEY. Store the secret name for a the step Configure local values file.kubectl create secret tls $TLSCONFIG --cert=$TLSCERT --key=$TLSKEYFor example, if
$TLSCONFIGiscust-cert-secretwith the certificate$TLSCERTisfullchain.pemand key$TLSKEYisprivkey.pem, then the command would be translated askubectl create secret tls cust-cert-secret --cert=fullchain.pem --key=privkey.pem
Default Helm Installation Settings
A default Helm install of Wallaroo contains various default settings. The local values file overwrites values based on the organization needs. The following represents the minimum mandatory values for a Wallaroo installation using certificates and the default LoadBalancer for a cloud Kubernetes cluster. The configuration details below is saved as values.yaml for these examples.
Note the following required settings:
wallarooDomain: Used to set the DNS domain name for the Wallaroo instance. For more information, see the Wallaroo DNS Integration Guide.custTlsSecretName: Specify the Kubernetes secret created in the previous step. External connections through the Wallaroo SDK require valid certificates.apilb: Sets theapilbservice options including the following:serviceType: LoadBalancer: Uses the default LoadBalancer setting for the Kubernetes cloud service the Wallaroo instance is installed into. Replace with the specific service connection settings as required.external_inference_endpoints_enabled: true: This setting is required for performing external SDK inferences to a Wallaroo instance. For more information, see the Wallaroo Model Endpoints Guidekubernetes_distribution: The cloud provider used. Each cloud provider has their own methods of handling storage classes, LoadBalancers (LB), etc. The following values are available; if your selected provider or distribution is not on the list, contact your Wallaroo Support representative for more options.aks: Microsoft Azure Kubernetes Serviceeks: Amazon Elastic Kubernetes Servicegke: Google Kubernetes Engineoke: Oracle Cloud Infrastructure Container Engine for Kuberneteskurl: On premise aka stand alone Linux installations.
ingress_mode: How the Wallaroo instance is reached through the Kubernetes network settings. Options include:internal(Default): An internal cloud load balancer and associated resources are created. Network users outside the Kubernetes cluster – but on the same internal network – can connect directly using DNS names, and do not need to use port forward or related configurations.external: An external, Internet-facing cloud load balancer, public IP, and associated resources are created. This is highly discouraged. Public DNS is also required. This is the default for Wallaroo Community Edition.none: Services are local to the Kubernetes cluster.kubectl-port forwardor some other means is required to access them. If all work will be done in-cluster, select this option.
dashboard: The name displayed when users login to the Wallaroo Ops center Dashboard. For example, “My Company” or “Sales Division”, etc.
The following example shows the minimum required options.
This example shows the uncommented keys for the minimum required settings and additional commented optional settings. For full details on helm values for Wallaroo installations, see the Wallaroo Helm Reference Guides.
wallarooDomain: "wallaroo.example.com" # change to match the actual domain name
custTlsSecretName: cust-cert-secret
apilb:
serviceType: LoadBalancer
external_inference_endpoints_enabled: true
ingress_mode: internal # internal (Default), external,or none
dashboard:
clientName: "Wallaroo Helm Example" # Insert the name displayed in the Wallaroo Dashboard
kubernetes_distribution: "" # Required. One of: aks, eks, gke, oke, or kurl.
# Enable edge deployment
#ociRegistry:
# enabled: true # true enables the Edge Server registry information, false disables it.
# registry: ""# The registry url. For example: reg.big.corp:3579.
# repository: ""# The repository within the registry. This may include the cloud account, or the full path where the Wallaroo published pipelines should be kept. For example: account123/wallaroo/pipelines.
# email: "" # Optional field to track the email address of the registry credential.
# username: "" # The username to the registry. This may vary based on the provider. For example, GCP Artifact Registry with service accounts uses the username _json_key_base64 with the password as a base64 processed token of the credential information.
# password: "" # The password or token for the registry service.
# Enable edge deployment observability
# edgelb:
# enabled: true
# The nodeSelector and tolerations for all components
# This does not apply to nats, fluent-bit, or minio so needs to be applied separately
# nodeSelector:
# wallaroo.ai/reserved: true
# tolerations:
# - key: "wallaroo.ai/reserved"
# operator: "Exists"
# effect: "NoSchedule"
# To change the pipeline taint or nodeSelector,
# best practice is to change engine, enginelb, and engineAux
# together unless they will be in different pools.
# engine:
# nodeSelector:
# wallaroo.ai/node-purpose: pipelines
# tolerations:
# - key: "wallaroo.ai/pipelines"
# operator: "Exists"
# effect: "NoSchedule"
# enginelb:
# nodeSelector:
# wallaroo.ai/node-purpose: pipelines
# tolerations:
# - key: "wallaroo.ai/pipelines"
# operator: "Exists"
# effect: "NoSchedule"
# engineAux:
# nodeSelector:
# wallaroo.ai/node-purpose: pipelines
# tolerations:
# - key: "wallaroo.ai/pipelines"
# operator: "Exists"
# effect: "NoSchedule"
# For each service below, adjust the disk size and resources as required.
# If the nodeSelector or tolerations are changed for one service,
# the other services nodeSelector and tolerations **must** be changed to match
#
#
# plateau:
# diskSize: 100Gi
# resources:
# limits:
# memory: 4Gi
# cpu: 1000m
# requests:
# memory: 128Mi
# cpu: 100m
# nodeSelector:
# wallaroo.ai/node-purpose: persistent
# tolerations:
# - key: "wallaroo.ai/persistent"
# operator: "Exists"
# effect: "NoSchedule"
# Jupyter has both hub and lab nodeSelectors and tolerations
# They default to the same persistent pool, but can be assigned to different ones
# jupyter:
# nodeSelector: # Node placement for Hub administrative pods
# wallaroo.ai/node-purpose: persistent
# tolerations:
# - key: "wallaroo.ai/persistent"
# operator: "Exists"
# effect: "NoSchedule"
# labNodeSelector: # Node placement for Hub-spawned jupyterlab pods
# wallaroo.ai/node-purpose: persistent
# labTolerations:
# - key: "wallaroo.ai/persistent"
# operator: "Exists"
# effect: "NoSchedule"
# memory:
# limit: "4" # Each Lab - memory limit in GB
# guarantee: "2" # Each Lab - lemory guarantee in GB
# cpu:
# limit: "2.0" # Each Lab - fractional CPU limit
# guarantee: "1.0" # Each Lab - fractional CPU guarantee
# storage:
# capacity: "50" # Each Lab - disk storage capacity in GB
# minio:
# persistence:
# size: 25Gi
# nodeSelector:
# wallaroo.ai/node-purpose: persistent
# tolerations:
# - key: wallaroo.ai/persistent
# operator: "Exists"
# effect: "NoSchedule"
# resources:
# requests:
# memory: 1Gi
# postgres:
# diskSize: 10Gi
# nodeSelector:
# wallaroo.ai/node-purpose: persistent
# tolerations:
# - key: "wallaroo.ai/persistent"
# operator: "Exists"
# effect: "NoSchedule"
# resources:
# limits:
# memory: 2Gi
# cpu: 500m
# requests:
# memory: 512Mi
# cpu: 100m
# Prometheus has the usual persistent options, but also a retention size
# The the size on disk and time can be configured before removing it.
# prometheus:
# storageRetentionSizeGb: "10" # Retain this much data, in GB.
# storageRetentionTimeDays: "15" # When to remove old data. In days.
# nodeSelector:
# wallaroo.ai/node-purpose: persistent
# tolerations:
# - key: "wallaroo.ai/persistent"
# operator: "Exists"
# effect: "NoSchedule"
# resources:
# limits:
# memory: 6Gi
# cpu: 2000m
# requests:
# memory: 512Mi
# cpu: 100m
# nats:
# podTemplate:
# merge:
# spec:
# nodeSelector:
# wallaroo.ai/node-purpose: persistent
# tolerations:
# - key: "wallaroo.ai/persistent"
# operator: "Exists"
# effect: NoSchedule
# wallsvc:
# nodeSelector:
# wallaroo.ai/node-purpose: persistent
# tolerations:
# - key: "wallaroo.ai/persistent"
# operator: "Exists"
# effect: "NoSchedule"
persistentVolume Settings
Wallaroo services that have a persistentVolume have the following default nodeSelector label and tolerations:
nodeSelector- Label:
wallaroo.ai/node-purpose - Value:
persistent
- Label:
tolerations- Key: wallaroo.ai/persistent
- Operator: “Exists”
- Effect: “NoSchedule”
For example:
nodeSelector:
wallaroo.ai/node-purpose: persistent
tolerations:
- key: wallaroo.ai/persistent
operator: "Exists"
effect: "NoSchedule"
If the nodeSelector or tolerations are changed for any service with a persistentVolume, all other services must be edited to match.
For additional information on taints and tolerations settings, see the Taints and Labels Guide.
Install Wallaroo with Helm
Install Wallaroo: The Wallaroo support representative will provide the installation command for the Helm install that will use the Wallaroo container registry. This assumes that the preflight checks were successful. This command uses the following format:
helm install $RELEASE $REGISTRYURL --version $VERSION --values $LOCALVALUES.yaml --timeout 10mWhere:
$RELEASE: The name of the Helm release. By default,wallaroo.$REGISTRYURL: The URl for the Wallaroo container registry service.$VERSION: The version of Wallaroo to install. For this example,2024.2.1.$LOCALVALUES: The .yaml file containing the local values overrides. For this example,values.yaml.
For example, for the registration
wallaroothe command would be:helm install wallaroo oci://registry.replicated.com/wallaroo/2024-2/wallaroo --version 2024.2.1 --values values.yaml --timeout 10mIf any required elements are missing from the
values.yamlfile, an error is displayed. For example, leaving out thekubernetes_distributionfield returns the following:Warning - kubernetes_distribution must be set in user provided values.yamlUpon successful installation, notes are published indicating the installed version, where to find documentation, etc.:
NOTES: . Welcome to Wallaroo 2024.2.0 1. Deployment Information: Name: 2024.2.0 Release notes: https://docs.wallaroo.ai/wallaroo-release-notes/wallaroo-release-202401 Version: v2024.2.0-5187 2. Accessing Wallaroo Documentation: https://docs.wallaroo.ai Dashboard: https://sample.wallaroocommunity.ninja 3. Useful Commands: - Helm tests are available by using: `helm test wallaroo`. - External load balancer hostname can be found by using: kubectl get svc api-lb-ext -n wallaroo -o jsonpath='{.status.loadBalancer.ingress[0].hostname}' - List Wallaroo namespaces, including pipeline deployments, but not including the main `wallaroo` namespace: kubectl get namespaces -l wallaroo-managed=true - In order to change any helm values: helm upgrade --install wallaroo oci://registry.replicated.com/wallaroo/uat-latest/wallaroo --version v2024.2.0-5187 --values $LOCALVALUES_YAML --timeout 10m 4. Uninstall: 1. To uninstall/delete the Wallaroo deployment, run: kubectl delete ns wallaroo && kubectl delete \ all,secret,configmap,clusterroles,clusterrolebindings,storageclass,crd \ --selector app.kubernetes.io/part-of=wallaroo --selector kots.io/app-slug=wallaroo 2. To delete all pipelines, run: kubectl delete ns -l wallaroo-managed=true .Verify the Installation: Once the installation is complete, verify the installation with the
helm test $RELEASEcommand. A condensed display usesegrepto show only the test suite and phase status as follows. Replacewallaroowith the name of thehelmrelease used.helm test wallaroo | egrep 'SUITE:|Phase:' TEST SUITE: wallaroo-fluent-bit-test-connection Phase: Succeeded TEST SUITE: nats-test-request-reply Phase: Succeeded TEST SUITE: wallaroo-wallaroo-test-connections-hook Phase: Succeeded TEST SUITE: wallaroo-test-objects-hook Phase: SucceededThe following will show the full
helmtest output with notes.helm test wallaroowhich displays the following:
NAME: wallaroo LAST DEPLOYED: Fri May 17 14:00:04 2024 NAMESPACE: wallaroo STATUS: deployed REVISION: 2 TEST SUITE: wallaroo-fluent-bit-test-connection Last Started: Fri May 17 14:04:48 2024 Last Completed: Fri May 17 14:04:51 2024 Phase: Succeeded TEST SUITE: nats-test-request-reply Last Started: Fri May 17 14:04:43 2024 Last Completed: Fri May 17 14:04:48 2024 Phase: Succeeded TEST SUITE: sample-wallaroo-test-connections-hook Last Started: Fri May 17 14:04:24 2024 Last Completed: Fri May 17 14:04:31 2024 Phase: Succeeded TEST SUITE: sample-wallaroo-test-objects-hook Last Started: Fri May 17 14:04:31 2024 Last Completed: Fri May 17 14:04:43 2024 Phase: Succeeded NOTES: . Welcome to Wallaroo 2024.2.0 1. Deployment Information: Name: 2024.2.0 Release notes: https://docs.wallaroo.ai/wallaroo-release-notes/wallaroo-release-202401 Version: v2024.2.0-5187 2. Accessing Wallaroo Documentation: https://docs.wallaroo.ai Dashboard: https://sample.wallaroocommunity.ninja 3. Useful Commands: - Helm tests are available by using: `helm test wallaroo`. - External load balancer hostname can be found by using: kubectl get svc api-lb-ext -n wallaroo -o jsonpath='{.status.loadBalancer.ingress[0].hostname}' - List Wallaroo namespaces, including pipeline deployments, but not including the main `wallaroo` namespace: kubectl get namespaces -l wallaroo-managed=true - In order to change any helm values: helm upgrade --install wallaroo oci://registry.replicated.com/wallaroo/2024-2/wallaroo --version 2024.2.1 --values $LOCALVALUES_YAML --timeout 10m 4. Uninstall: 1. To uninstall/delete the Wallaroo deployment, run: kubectl delete ns wallaroo && kubectl delete \ all,secret,configmap,clusterroles,clusterrolebindings,storageclass,crd \ --selector app.kubernetes.io/part-of=wallaroo --selector kots.io/app-slug=wallaroo 2. To delete all pipelines, run: kubectl delete ns -l wallaroo-managed=true .
At this point, the installation is complete and can be accessed through the fully qualified domain names set in the installation process above. Verify that the DNS settings are accurate before attempting to connect to the Wallaroo instance. For more information, see the Wallaroo DNS Integration Guide.
To add the initial users if they were not set up through Helm values, see the Wallaroo Enterprise User Management guide.
Required Installation Configurations
Once installed, the following actions are required settings are required to complete the setup process process.
DNS Services Integration
DNS services integration is required for Wallaroo Enterprise to provide access to the various supporting services that are part of the Wallaroo instance. These include:
- Simplified user authentication and management.
- Centralized services for accessing the Wallaroo Dashboard, Wallaroo SDK and Authentication.
- Collaboration features allowing teams to work together.
- Managed security, auditing and traceability.
The following guide is for standard DNS services.
Once integrated, users can access the following services directly from a URL starting with the Wallaroo Domain - this is the domain name the DNS enetry is set to. For example, if the Wallaroo Domain is wallaroo.example.com, then the Wallaroo Ops instance is accessed from https://wallaroo.example.com/{service}.
Note that even when accessing specific Wallaroo services directly that the user must authenticate through Wallaroo or another authorized authentication service.
| Service | Path | Description |
|---|---|---|
| Wallaroo Dashboard | wallaroo domain | Provides access to a user interface for updating workspaces, pipelines, and models. Also provides access to the integrated JupyterHub service. |
| API | v1/api | Provides access to the Wallaroo API. For example, wallaroo.example.com/v1/api. |
| Authentication | auth | Access to authentication management including SSO configurations. For example: wallaroo.example.com/auth. For details on user management, see Wallaroo User Management. For details on user management services, see Wallaroo Authentication Configuration Guides. |
| Edge Observability | edge | Optional service for edge and multicloud deployments to report inference results back to the Wallaroo Ops instance. For example: wallaroo.example.com/edge. |
Prerequisites
- Install Wallaroo Enterprise into a qualified environment. For more details, see the Wallaroo Install Guides and the Wallaroo Enterprise Install Guides.
- Generate or update the the SSL Certificates
- Have access to internal corporate DNS configurations that can be updated. A subdomain for the Wallaroo instance will be created through this process.
- Have the IP address for the Wallaroo instance.
- Install kubectl into the Kubernetes cluster administrative node.
Wallaroo IP Address Retrieval Methods
The first step is to retrieve the IP address that is set to the DNS services.
Retrieve LoadBalancer IP with kubectl
For most organizations that install Wallaroo into a cloud based Kubernetes cluster such as Microsoft Azure, AWS, etc the external IP address is tied to Wallaroo LoadBalancer service. This can be retrieved with the kubectl command as follows:
Retrieve the external IP address for your Wallaroo instance LoadBalancer. For example, this can be performed through the following
kubectlcommand:kubectl get svc api-lb-ext -n wallaroo -o jsonpath='{.status.loadBalancer.ingress[0].ip}' 34.83.140.98Verify that the IP address is the one that is used either for clusters in an internal or external mode.
An alternative to this command to show all services is the following:
kubectl get svc -AExample Result:
kubectl get svc -A NAMESPACE NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE default kubernetes ClusterIP 10.25.64.1 <none> 443/TCP 50d gmp-system alertmanager ClusterIP None <none> 9093/TCP 50d gmp-system gmp-operator ClusterIP 10.25.70.18 <none> 8443/TCP,443/TCP 50d kube-system default-http-backend NodePort 10.25.67.38 <none> 80:31378/TCP 50d kube-system kube-dns ClusterIP 10.25.64.10 <none> 53/UDP,53/TCP 50d kube-system metrics-server ClusterIP 10.25.67.8 <none> 443/TCP 50d wallaroo alertconfig ClusterIP 10.25.67.141 <none> 9094/TCP 2m30s wallaroo alertmanager ClusterIP 10.25.77.167 <none> 9093/TCP 2m30s wallaroo api-lb ClusterIP 10.25.79.188 <none> 8080/TCP 2m31s wallaroo api-lb-admin ClusterIP 10.25.70.0 <none> 9901/TCP 2m31s wallaroo api-lb-ext LoadBalancer 10.25.69.9 34.83.140.98 80:30715/TCP,443:32664/TCP 2m31s wallaroo dashboard ClusterIP 10.25.72.14 <none> 4567/TCP 2m31s wallaroo wallsvc ClusterIP 10.25.75.74 <none> 3040/TCP 2m30sSome cloud providers may provide multiple external IP addresses for the
api-lbservice. For some services such as Oracle, this is typically a 10 net address, with the second IP address being the actual external address. Verify the IP address before changing DNS settings.
Other Methods
For organizations that install Wallaroo other methods, such as Single Node Linux may find the kubectl get svc api-lb-ext command only returns the internal IP address.
Depending on the instance, there are different methods of acquiring that IP address. The links below reference difference sources.
- AWS: How do I get the ID and IP address of an Amazon EC2 instance for an AWS Batch job?
- GCP: Locating IP addresses for an instance
- Azure: IP addresses in Azure Functions
Refer to your Wallaroo support representative if further assistance is needed.
DNS Entries
Create DNS the following entries based on the list above for the Wallaroo instance’s IP address. Select the cloud environment used for DNS services.
- For AWS Clusters:
- Wallaroo domain: CN (CNAME) record referring to the AWS EKS cluster endpoint. For example:
wallaroo.example.com.
- Wallaroo domain: CN (CNAME) record referring to the AWS EKS cluster endpoint. For example:
- For all other cloud services:
- Wallaroo domain:
Arecord,NS(Name Server) record,SOA(Start Of Authority) record. For example:wallaroo.example.com
- Wallaroo domain:
- References:
Edge Observability Enablement
For organizations that deploy Wallaroo pipelines on edge devices as Wallaroo Servers, see the DNS settings from the Edge Deployment Registry Guide.
Setup Users
User management is managed through the Wallaroo Dashboard, via the Platform Admin Dashboard page. See the Wallaroo User Management for full guides on setting up users, identity providers, and other user configuration options.
The following is an abbreviated guide on setting up new Wallaroo users.
IMPORTANT NOTE
At least one user must be created before using Wallaroo.The process includes the following steps:
Obtain the User Admin Credentials
Obtaining the admin User Credentials
The standard Wallaroo installation creates the user admin by default and assigns them a randomly generated password. The admin user credentials are obtained which may be obtained directly from Kubernetes with the following commands, assuming the Wallaroo instance namespace is wallaroo.
Retrieve Admin Username
kubectl -n wallaroo \ get secret keycloak-admin-secret \ -o go-template='{{.data.KEYCLOAK_ADMIN_USER | base64decode }}'Retrieve Admin Password
kubectl -n wallaroo \ get secret keycloak-admin-secret \ -o go-template='{{.data.KEYCLOAK_ADMIN_PASSWORD | base64decode }}'
Create a New User with the Admin Role
Creating users is managed through the Platform Admin Dashboard. The following steps are used to create an initial user with the role admin.
- Access the Wallaroo Dashboard through the DNS name set up in the DNS Services Integration step. For example, if the DNS name of the Wallaroo Ops center is
wallaroo.example.com, the Wallaroo Dashboard is available athttps://wallaroo.example.com. - Login with the username
adminand the password retrieved in Obtaining the admin User Credentials. - Select Create Users and enter the following:
- User Email: The email address for the user. This must be in the valid email address format.
- Assign Type: Select Admin.
- Password: Enter the user’s password. This user password be sent to the new user.
- Temporary or Permanent:
- Temporary: The user will be forced to change their login password upon their next login (Recommended).
- Permanent: The user will keep their password.
- Create any additional users as needed. When finished, select the Wallaroo icon drop down and select Logout.
At this point, users can log in to Wallaroo Dashboard with their provided identities. For guides on setting up Single Sign-On (SSO) and other features, see Wallaroo User Management for full guides on setting up users, identity providers, and other user configuration options.
Next Steps
Ready for more? Time to deploy models and start inferencing.
- See the Wallaroo 101 for a run through of uploading, deploying, and inferencing on ML models.
- For Large Language Models, see the Large Language Models Operations guides.
- For edge and multi-cloud deployments, see the Run Anywhere Tutorials for instructions on deploying ML models in any cloud, any architecture, on any platform.
For access to these sample models and a demonstration on using LLMs with Wallaroo:
- Contact your Wallaroo Support Representative OR
- Schedule Your Wallaroo.AI Demo Today